This section supplements the “LIS-SV”
product manual. The parameters described here are only available if the LIS-SV
is used in an ABULiner control unit.
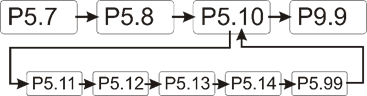
Overview of the
'ABULiner' parameter level
The following parameters can be set in the 'ABULiner'
parameter level of the LIS-SV.
|

|
Danger during setting work!
During setting work on the LIS-SV, monitoring of
the wire rope hoist is switched off. This means the wire rope hoist cannot
be monitored for excess load, among other things. This means the
wire rope hoist cannot be monitored for excess load, among other
things.
This in turn means the load could fall and kill or
injure people!
Do not use the crane for normal work during
setting work, and only lift loads very carefully for test
purposes! |
All LIS-SV parameters which are important for the ABULiner
are combined in a separate parameter level, which is shown as a submenu.
 Move the load hook out of
the limit switch range (up or down).
Move the load hook out of
the limit switch range (up or down).
During parameter setting, the load hook must not be within the
limit switch range.
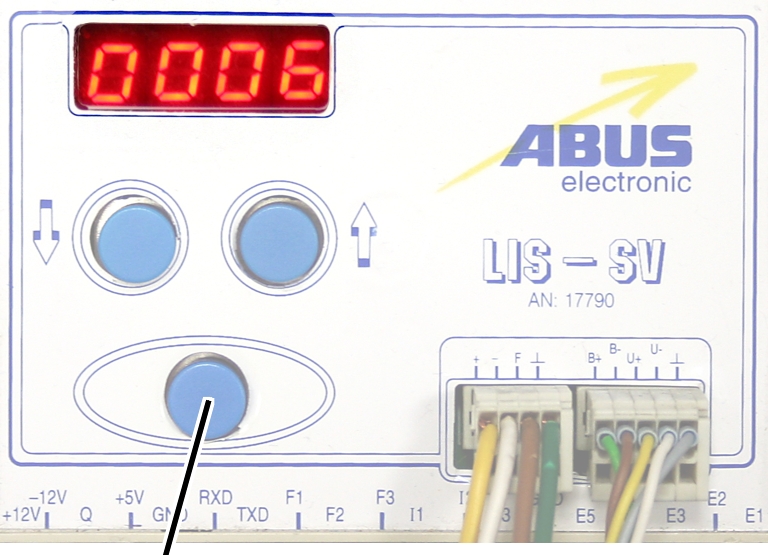
 Open the menu of the
LIS-SV. See the documentation “Load indicator system LIS-SV”.
Open the menu of the
LIS-SV. See the documentation “Load indicator system LIS-SV”.
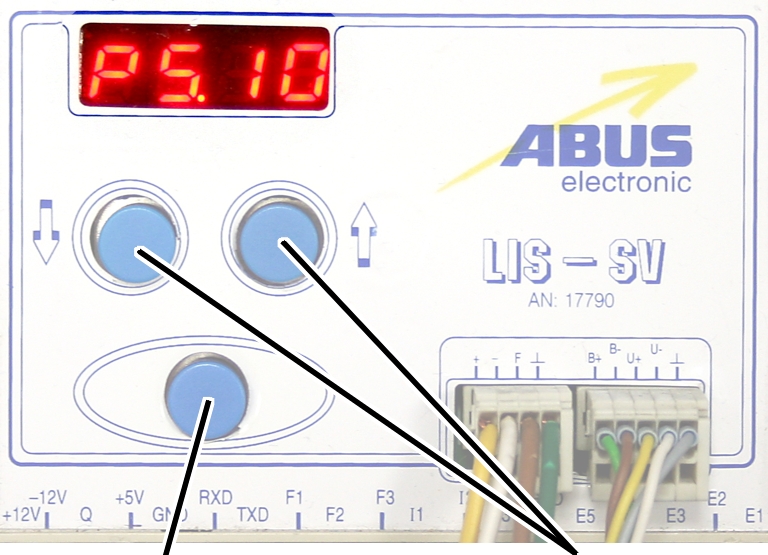
|
|
|
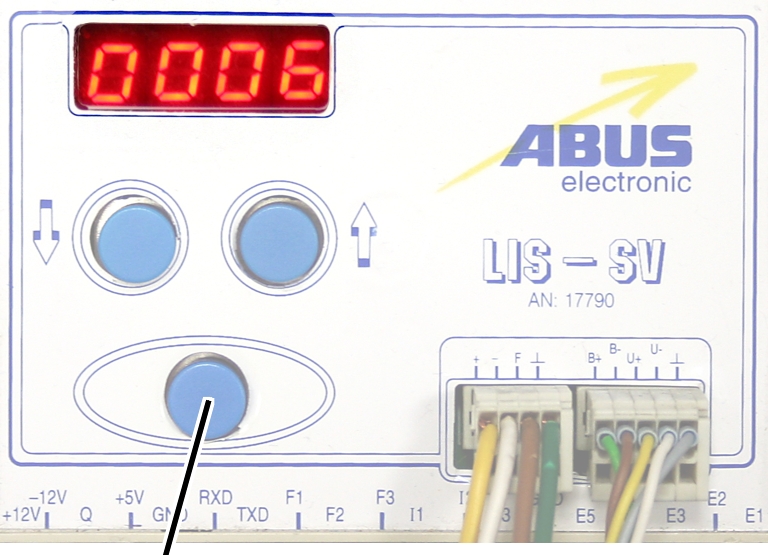
Enter
button |
Arrow
buttons |
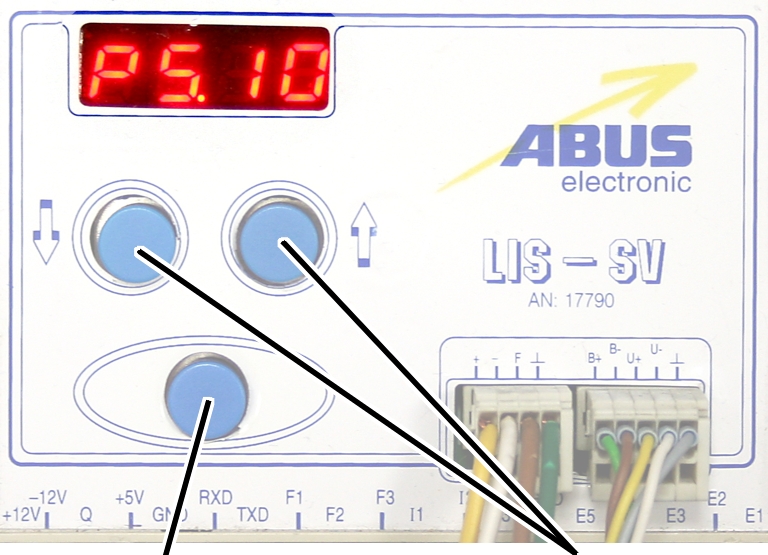
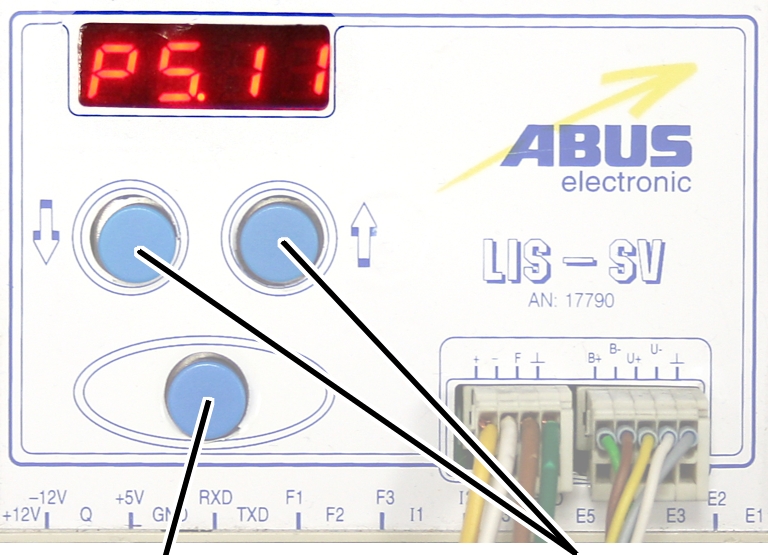
 Select parameter 5.10.
Select parameter 5.10.
 Press ENTER.
Press ENTER.
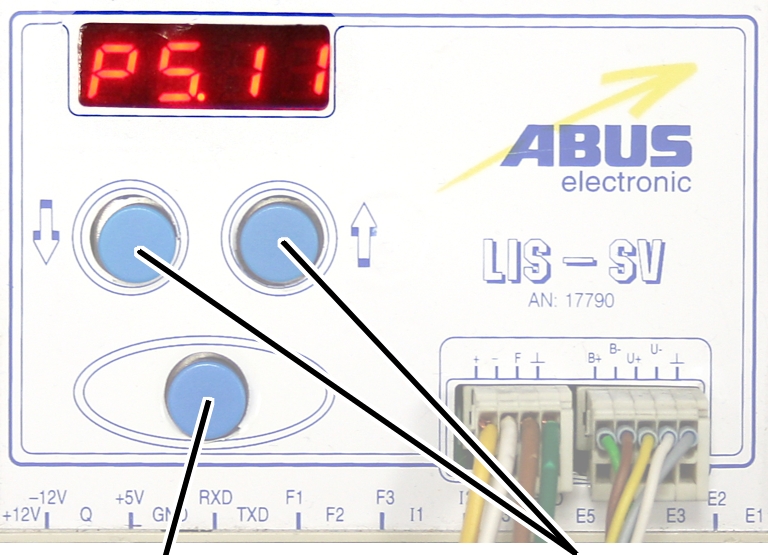
● The
'ABULiner' parameter level is activated.
● Parameter
5.11 is displayed.
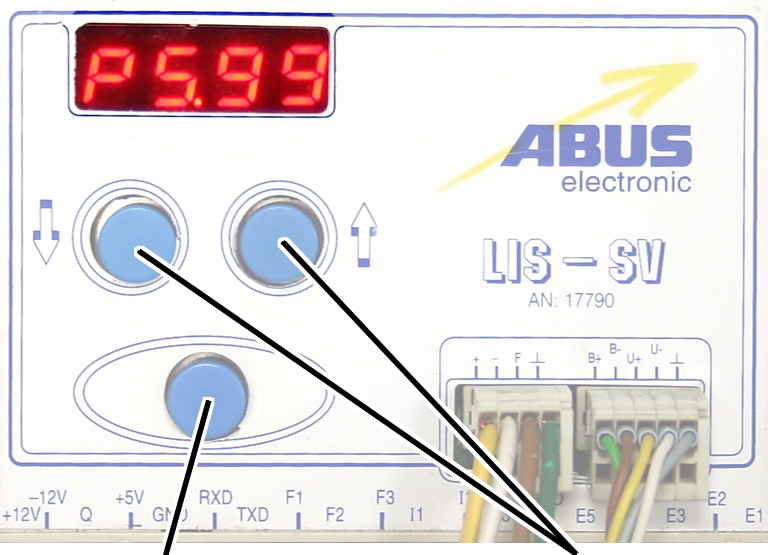
Exiting the
'ABULiner' parameter level
|
|
|
Enter
button |
Arrow
buttons |
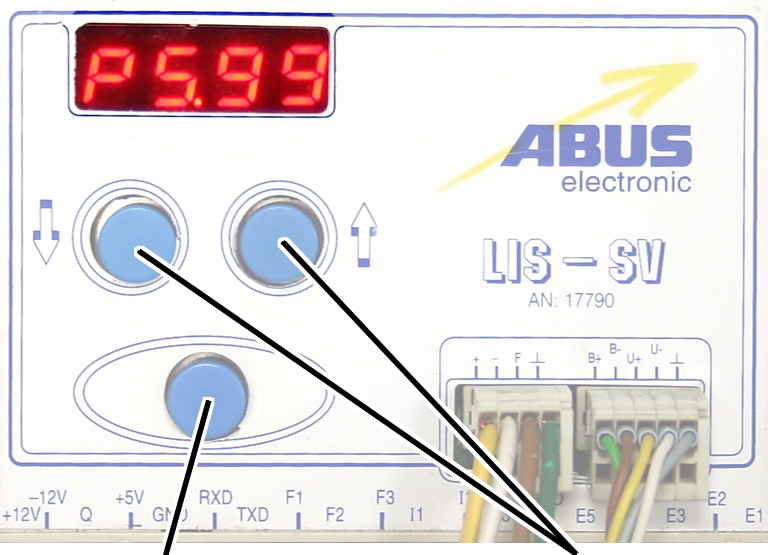
 Select parameter 5.99.
Select parameter 5.99.
 Press ENTER.
Press ENTER.
● The
previous parameter level is reactivated.
● Parameter
5.10 is displayed.
The LIS-SV is automatically activated for the ABULiner if a
value is entered for the parameter 5.11.
In the ABULiner mode (a value is set for parameter 5.11):
─ The
LIS-SV can monitor the total load for a maximum of two wire rope hoists.
─ Input F3
(normally used for measuring the load of wire rope hoist 3) now serves in
monitoring the current rotational frequency of the hoist motor.
─ A value
can be entered for parameter 3.0 (maximum load capacity of wire rope hoist 3).
If a value is entered for this, parameter 5.11 cannot be set.
─ This
interlocking thus excludes an incorrect setting.
─ The
load-controlled switching point at output TxD of the LIS-SV cannot be used.
─
Parameter 4.5 (setting for load-controlled switching point) is not available.
In the normal mode (no value is set for parameter 5.11):
─
Operation of the ABULiner Lifting/Lowering unit is not possible.
─ The
LIS-SV can monitor the total load for up to three wire rope hoists.
─ Input F3
serves in measuring the load of a third wire rope hoist.
─ A value
can be entered for parameter 5.11 (gear ratio). If a value is entered for this,
parameter 3.0 cannot be set.
─ This
interlocking thus excludes an incorrect setting.
─ The
load-controlled switching point at output TxD of the LIS-SV can be used.
─
Parameter 4.5 (setting for load-controlled switching point) can be used.
The LIS-SV uses the signal of the encoder and the gear ratio
of the hoisting gear to calculate the hook travel distance, the maximum distance
in the limit switch range and the current rotational frequency of the hoist
motor. The gear ratio must be set on the machine.
|
|
|
Cable
speed |
|
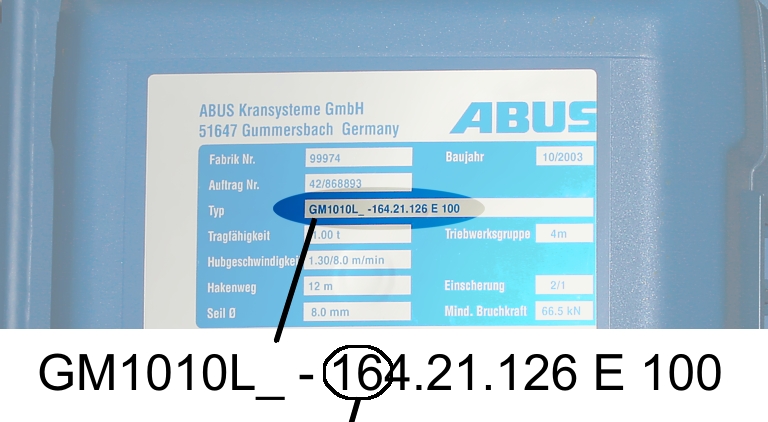
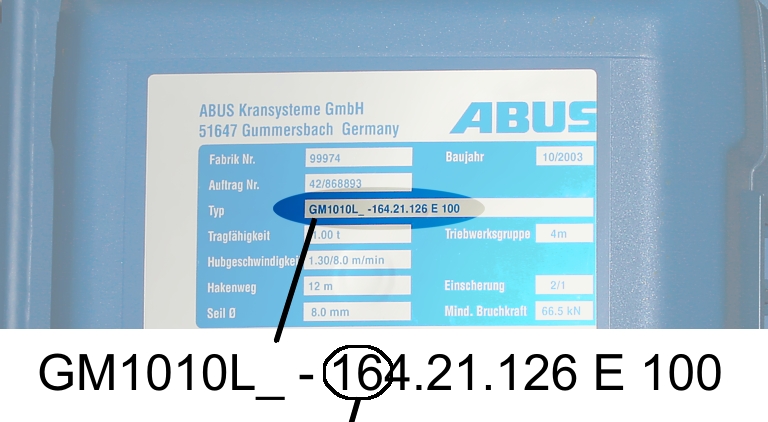
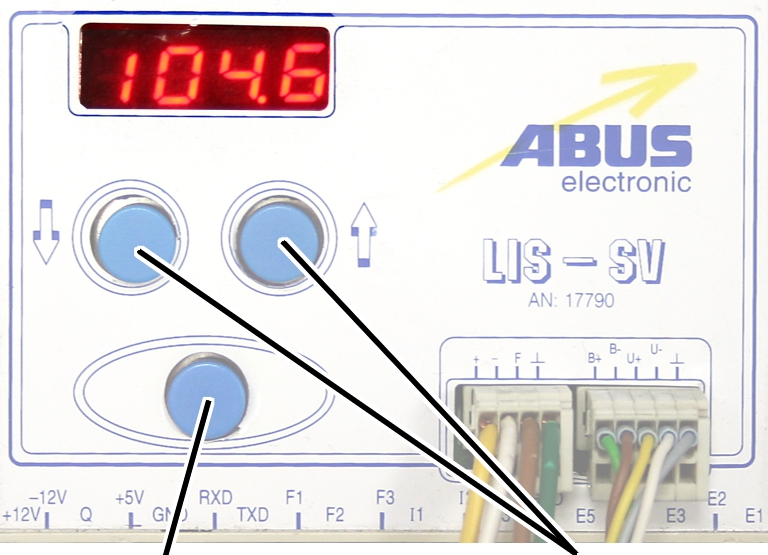
 Read off the type
designation at the type plate of the wire rope hoist.
Read off the type
designation at the type plate of the wire rope hoist.
 Read off the cable
speed.
Read off the cable
speed.
 From this table, select
the gear ratio that matches the cable speed.
From this table, select
the gear ratio that matches the cable speed.
|
|
Cable
speed |
|
Hoist motor GM |
32 m/min at 50 Hz
38 m/min at 60
Hz |
25 m/min at 50 Hz
30 m/min at 60
Hz |
20 m/min at 50 Hz
24 m/min at 60
Hz |
16 m/min at 50 Hz
19 m/min at 60
Hz |
|
800.4 |
50.01 |
63.49 |
77.77 |
98.16 |
|
800.5 |
47.03 |
60.04 |
74.66 |
95.03 |
|
1000.6 |
54.43 |
68.91 |
84.00 |
105.1 |
|
1000.7 |
54.60 |
68.06 |
81.45 |
104.6 |
|
2000.3 |
58.22 |
74.23 |
91.19 |
118.4 |
|
3000.4 |
73.61 |
93.92 |
118.4 |
152.9 |
|
5000.3 |
85.14 |
109.3 |
132.8 |
169.0 |
|
5000.4 |
80.20 |
104.9 |
127.7 |
160.6 |
|
6000.3 |
94.69 |
118.5 |
149.6 |
182.7 |
|
7000.1 |
118.0 |
148.3 |
182.6 |
232.0 |
|
|
|
|
|
|
Table: Gear ratios (numerical values) depending on
hoist motor (lines) and cable speeds (columns) at 50 and 60 Hz.
|
|
|
Enter
button |
Arrow
buttons |
 Move the load hook out of
the limit switch range (up or down).
Move the load hook out of
the limit switch range (up or down).
During parameter setting, the load hook must not be within the
limit switch range.
 Select parameter 5.11.
Select parameter 5.11.
 Press ENTER.
Press ENTER.
● The set
value is displayed.
If the value is 0.00, the function is deactivated.
● Hold ENTER
pressed.
● CODE is
displayed.
 Hold ENTER pressed.
Hold ENTER pressed.
|
|
|
Enter
button |
Arrow
buttons |
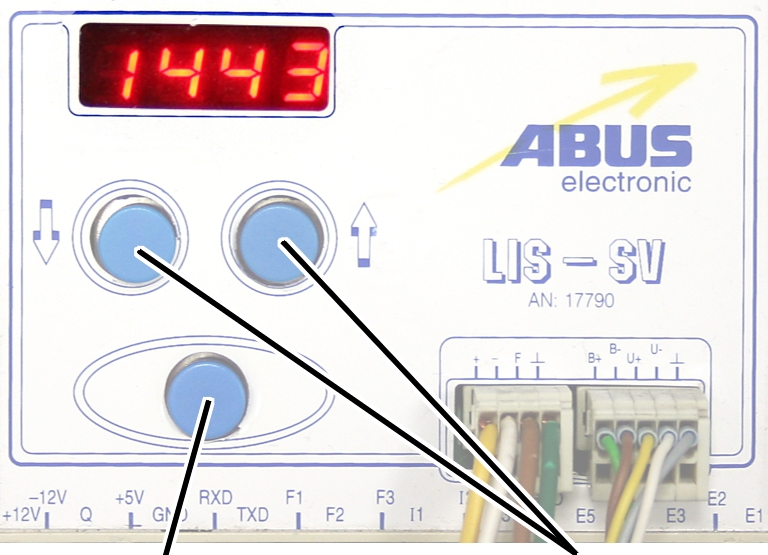
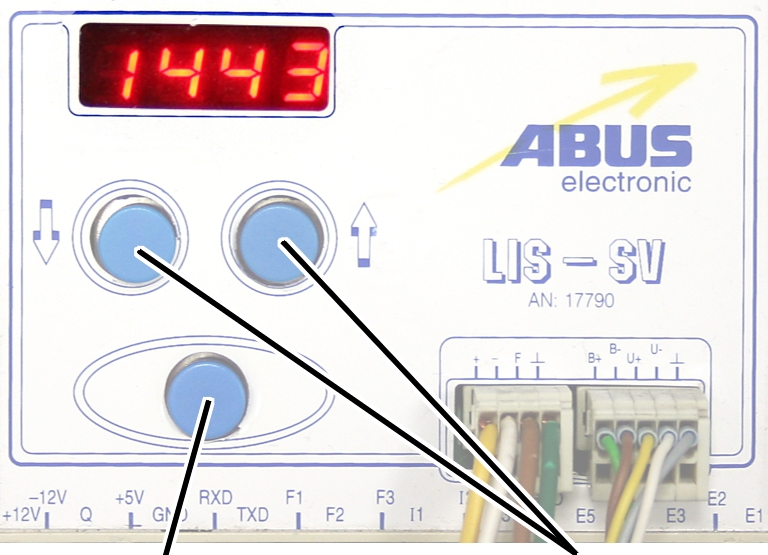
 Enter the code 1443.
Enter the code 1443.
 Press ENTER briefly.
Press ENTER briefly.
|
|
|
Enter
button |
Arrow
buttons |
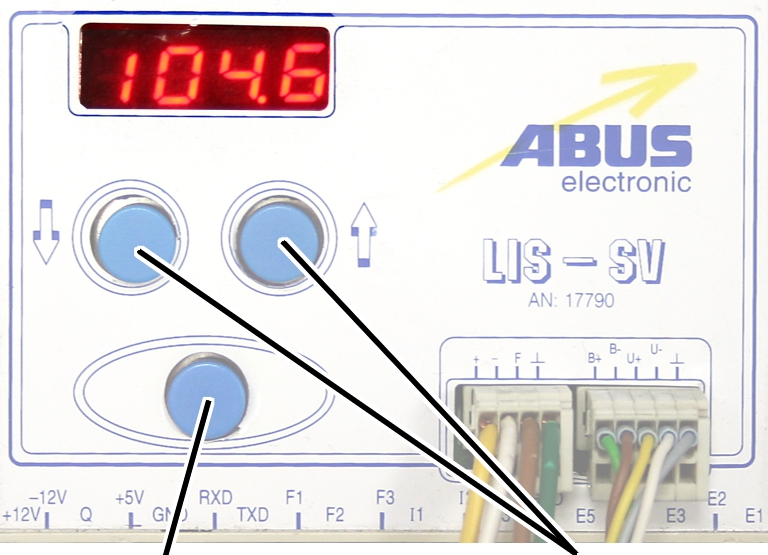
 Set the value from the
table.
Set the value from the
table.
If the display ‘0.00’ cannot be changed, a value is set in
parameter 3.0. In this case, set the value to zero first.
 Press ENTER briefly.
Press ENTER briefly.
Devils-night-party.zip — Full HD
I need to make sure the report is complete but concise. Maybe include timestamps, file paths, hashes (MD5, SHA1, SHA256) for verification. Also, if possible, check the file's reputation scores from online databases.
Wait, but I need to make sure that the report is thorough but not overly technical for those who might read it. Balance between the technical details and layman's terms. Maybe include a section on risk assessment, labeling the file as high risk if it's proven malicious, medium if it's suspicious, or low if it's benign. Also, recommend actions like isolating the file, notifying the relevant parties, and educating users on safe practices.
I should structure the report with an executive summary, detailed analysis, findings, and a conclusion. Make sure to include both the steps taken and the results. If there's no clear threat, still document that. Maybe mention that without further analysis in a secure environment, the risk can't be fully assessed. Also, note that opening attachments from unknown sources is a best practice to avoid. Devils-Night-Party.zip
I should mention common indicators of compromise (IOCs) like unexpected file types, hidden extensions, or odd directory structures. If it's a legitimate zip, maybe it has images, videos, or scripts related to a themed party. But if it's malicious, maybe it contains an executable with a benign name or a script that runs on extraction. Tools like 7-Zip, VirusTotal, or sandbox environments could be useful.
I should also think about how to present the findings clearly. For example, if scanning with VirusTotal shows no positives, that's important. If there are positives, list them. Also, mention any known malware families that match the file's characteristics. Maybe use a malware analysis report template for structure. I need to make sure the report is complete but concise
Also, the report should document the analysis process: initial observation, technical analysis, threat assessment, and recommendations. Need to highlight if anything suspicious was found, like a PowerShell script payload or a malicious LNK file. Maybe check for file sizes that are too large or too small for the content, which could indicate something's off.
In the end, summarize whether the file is safe or not, based on the analysis, and provide actionable steps for next steps. If it's malicious, how to remove it or contain it. If unclear, maybe recommend further analysis in a secure lab. Wait, but I need to make sure that
I should start by checking the file's origin. Where did it come from? If it was received in an email, maybe it's a phishing attempt. If it's from a download, perhaps a torrent or a shady website. The name is pretty generic, so it could be a malicious file disguised as something else. I need to consider file analysis steps: checking the hash, scanning with antivirus engines, examining the contents without extracting, then safely extracting and inspecting individual files.
So, in the analysis, I'd note the file contents, check each file's properties, MIME types, file headers to see if they match the expected type. Also, look for macros if there are .doc or .xls files inside. Maybe if there's a script or payload, check for obfuscation techniques or encoded commands.
Another point: sometimes .zip files are used to distribute malware, especially if they contain unexpected files like .exe extensions hidden as .zip because Windows might hide extensions. So need to check for that. For example, a file named "music.mp3.exe" which Windows shows as "music.mp3", which a user might run without realizing.
Only for auxiliary fans
The auxiliary fan of the hoist motor continues to run for
several minutes after the lifting or lowering. This ensures that the hoist motor
is adequately cooled even at slow lifting speeds. The run-on time can be
adjusted.
|
|
|
Enter
button |
Arrow
buttons |
 Move the load hook out of
the limit switch range (up or down).
Move the load hook out of
the limit switch range (up or down).
During parameter setting, the load hook must not be within the
limit switch range.
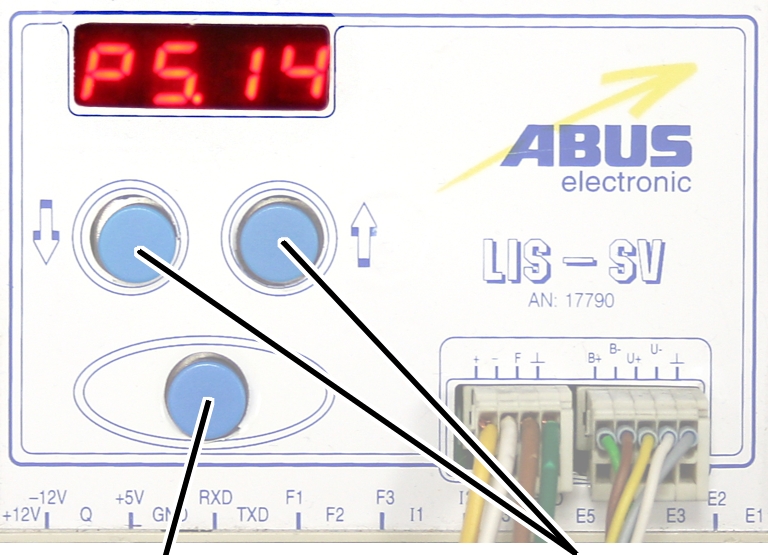
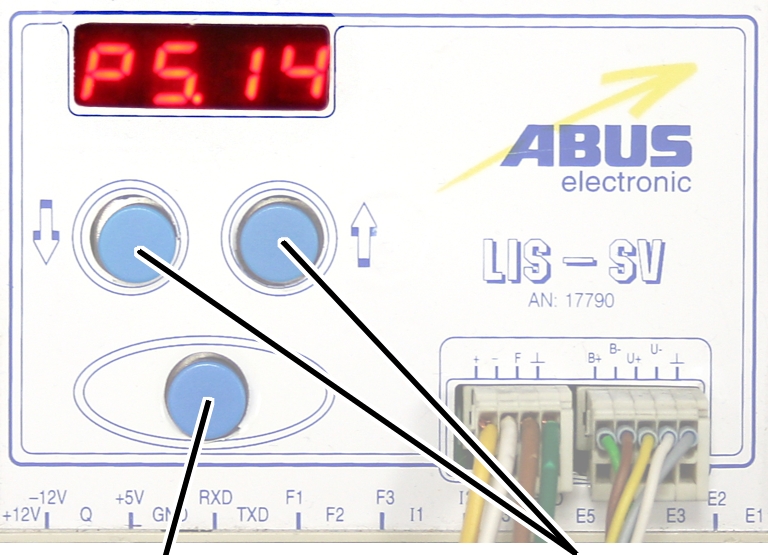
 Select parameter 5.14.
Select parameter 5.14.
 Press ENTER.
Press ENTER.
● The set
value is displayed.
|
|
|
Enter
button |
|
 Set the value to between 3
and 10 minutes using the arrow buttons.
Set the value to between 3
and 10 minutes using the arrow buttons.
 Press ENTER.
Press ENTER.